In order to remember hackers and offer protection to the Community infrastructure you will have to assume like a hacker in these days’s expansive and eclectic web and also you will have to needless to say not anything is totally secured.
Taking into account that you’re making ready to was an Moral Hacker, IT Safety Analyst, IT Safety Engineer, or a Cybersecurity Professional, but nonetheless unsure and need to learn about Firewalls, Intrusion Detection Programs, Intrusion Prevention Programs or Honeypots, you are going to to find this e-book extraordinarily helpful.
In the event you try to use any of the equipment or ways mentioned on this e-book on a Community with out being approved and also you disturb or harm any Programs, that may be thought to be unlawful black hat hacking. So, I want to inspire all readers to installation any device and means defined on this e-book for WHITE HAT USE ONLY.
The principle center of attention of this e-book is that will help you remember how Firewalls, Intrusion Detection Programs, Intrusion Prevention Programs or Honeypots paintings.
Your studying of this e-book will spice up your wisdom on What’s conceivable in these days’s hacking international and can help you to develop into an Moral Hacker aka Penetration Tester.
BUY THIS BOOK NOW AND GET STARTED TODAY!
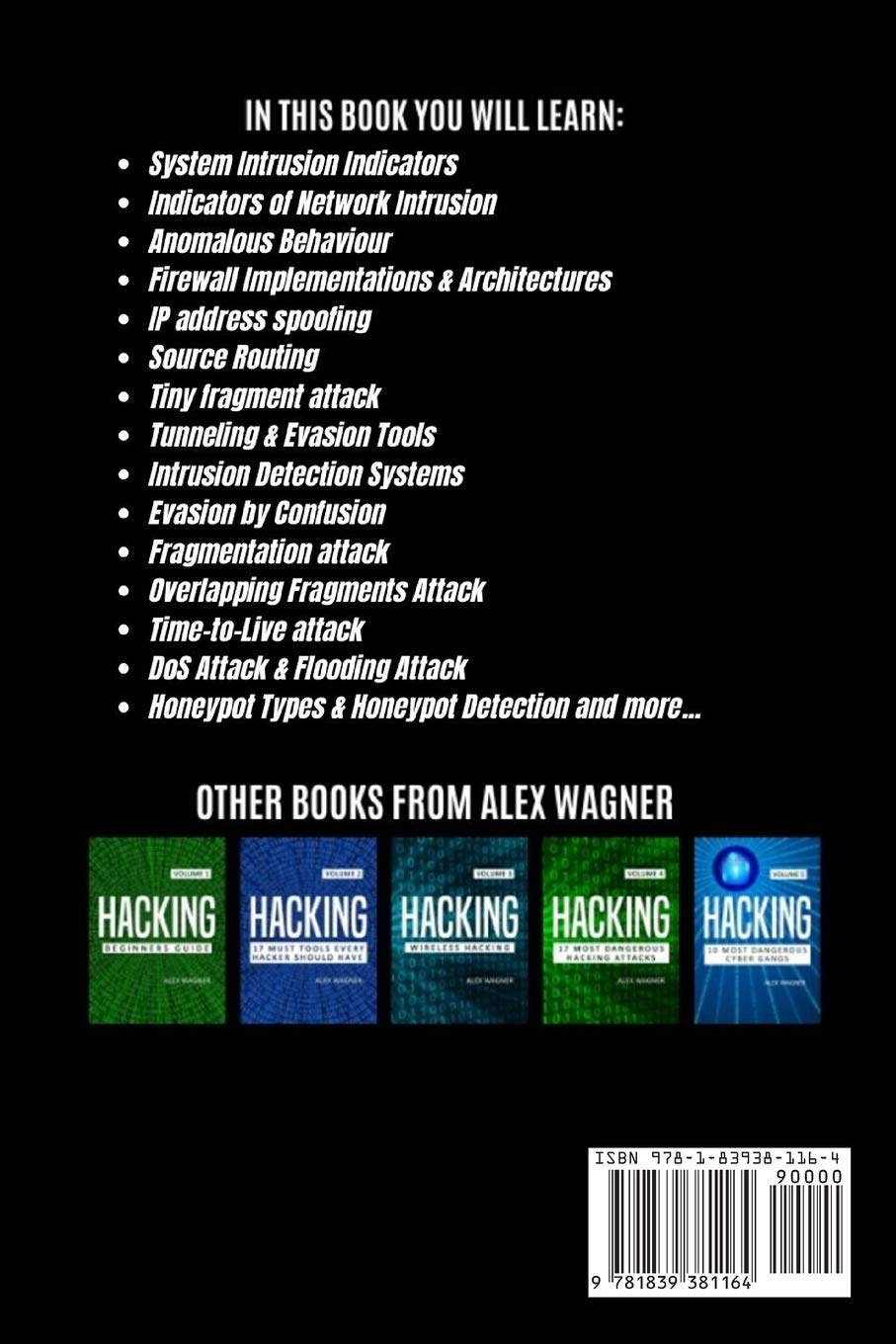
IN THIS BOOK YOU WILL LEARN ABOUT:
-What’s The OSI Model
-What are Zone Primarily based Firewalls
-Firewall Habits and TCP State Table
-Community Cope with Translation
-Port Cope with Translation
-Demilitarized Zone
-TCP & UDP Site visitors on Firewalls
-Shopper Connection Process
-Gadget Intrusion Indicators
-Signs of Community Intrusion
-Anomalous Behaviour
-Firewall Implementations & Architectures
-Packet Filtering Firewalls
-Circuit-degree Gateway
-Utility Firewalls
-Stateful Firewalls
-Subsequent-Gen Firewalls
-Detecting Firewalls
-IP Cope with spoofing
-Supply Routing
-Tiny fragment attack
-Tunneling
-Evasion Tools
-Intrusion Detection Systems
-Signature-Primarily based IDS
-Statistical Anomaly-Primarily based IDS
-Community-Primarily based IDS
-Host Intrusion Detection System
-Evasion via Confusion
-Fragmentation attack
-Overlapping Fragments Attack
-Time-to-Are living attack
-DoS Assault & Flooding Attack
-IDS weak spot Detection
-Honeypot Sorts & Honeypot Detection
BUY THIS BOOK NOW AND GET STARTED TODAY!